What is Cybersecurity
- Cybersecurity refers to the technologies and processes designed to protect computers networks and data from unauthorized access, vulnerabilities and attacks delivered via the internet by cybercriminals.
What are Cybersecurity standards
- Cybersecurity standards are security standards that enable us to practice safe security techniques to minimize the number of successful cybersecurity attacks.
What are other kinds of security that are available in the similar context
- Communication security – this means protecting the communication media, technology, and content.
- Network Security – this means protection of networking components and connection.
- Information security – this means the protection of all critical elements. This is the bigger umbrella under which all small systems fall in.
Definition and history of Cybercrime
- When an illegal activity takes place in Cyberspace that is called Cybercrime.
- The first recorded cybercrime was recorded in the year 1820.
- The first spam email took place in 197 when it was sent over the Arpanet.
- The first virus was installed on an Apple computer in 1982.
Different kinds of security problems
- Virus
- This is a program that is loaded onto your system without your knowledge and runs without your permission and wishes.
- Hacker
- This is a person who breaks into computers usually by gaining access to administrative controls.
- There are three types of Hackers
- White Hat
- Grey Hat
- Black Hat
- Malware
- This comes from the term Malicious Software.
- This is usually any software that infects and damages a computer system without the owner’s knowledge or permission.
- Trojan Horses
- These are email viruses that duplicate themselves, steal information or harm the computer system.
- These viruses are the most serious threats to computers.
- Password Cracking (The easiest)
- This is what most of the hackers use, and they can determine passwords that are easy by trying several combinations and they find passwords to several protected electronic areas like Bank accounts etc and Social Networking sites.
What should we do to protect?
- Read privacy policies in websites carefully when submitting data through the internet
- Use SSL to encrypt data and avoid interacting with sites that do not have SSL installed.
- Disable remote connectivity as much as possible.
- Have unique passwords for each account online. And use strong passwords always.
- Use a tool that will remember our passwords instead of us remembering the passwords and making ourselves vulnerable.
- Keep virus definitions of Antivirus software up to date.
- Do not download any software and install them from any website or platform.
- Change passwords from websites as frequently as possible.
- Insert firewalls and use popup blockers.
- Uninstall any unnecessary software from your computer.
- Always maintain backups of important data.
- Open attachments from senders you trust and know.
Myths that exist:
- If we use all precautions even if we are online, we are not prone to cyber-attack.
- Strong and different passwords for each website does not mean ease of access.
- This is not the responsibility of an employee but an employer.
Role of Social Media in Cybersecurity:
We are increasingly becoming more social in this connected world and companies now must find new ways to protect personal information. While social media plays a huge role in this, personal commitment to stay secure is even more important than ever. We are in a world right now that personal information stays with us is no more a thing.
Even though companies and organizations cannot stop using social media there should now be a more thoughtful approach to it. When some information is asked, the question should be thought through and asked the user then simply asking their information.
Both, the organizations asking the information and users who are providing this information could be more responsible towards the data collected and how it is stored then we surely can avoid being prey to the cybercriminals.
Different Cybersecurity Techniques that could be implemented:
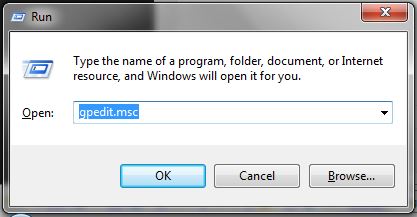
- Access control and password policy: this is one of the simplest things that anyone could do to ensure that they have a strong password and they use their password for each account they have. They should not be using duplicate passwords for several accounts. History has proved that this is our weakest link between what we think of passwords and we might not be as important for hackers but that has been proven to be wrong.
- Authentication of Data: we must always be authenticated before downloading any kind of data from any system or website. Usually, authentication and verification are done after one has downloaded the files, however on the server-side as well there should be validation that ensures that the downloadable artefact is not being downloaded by anybody and everybody.
- Malware scanners: Usually malware scanners scan all the documents and files that exist in a system for any virus. Viruses, worms, and Trojan Horses are examples of malicious software that are often grouped and referred to as malware. We should always have malware scanners in our systems to scan our system and identify the malware at regular intervals.
- Firewalls: A firewall is a software program or piece of hardware that helps screen out hackers and viruses. All messages entering and leaving the internet should go through a firewall, that way all the systems will be secure. Firewall plays a very important role in making systems secure.
- Antivirus software: This is another type of computer program which detects, prevents, and takes action to disarm or remove malicious software programs such as viruses and worms. Most antivirus programs include an auto-update feature that enables you to use the latest virus definitions to secure your system. We should always use legitimate software and make sure that it has the latest virus definitions so that it could safeguard us. Anti-virus software is a must and basic need for every system we could say.
Computer security is a vast topic that is becoming more important because the world is becoming highly interconnected, with networks being used to carry out critical transactions. Cybercrime continues to diverge down different paths with each New Year that passes and so does the security of the information. The latest and disruptive technologies, along with the new cyber tools and threats that come to light each day, are challenging organizations with not only how they secure their infrastructure, but how they require new platforms and intelligence to do so. There is no perfect solution for cyber-crimes, but we should try our level best to minimize them to have a safe and secure future in cyberspace.
Here are some of our trending articles that might interest you:

I am a 33-year-old gentleman from a lower-middle-class family hailing from a small village Narasinghpur in Cuttack, Odisha, INDIA. I have a post-graduate degree in M.Tech from BITS Pilani. I started blogging back in June 2014. You can check out my journey and all that I have learnt all these years on my website.